“We all obsess over growth, but what about the silent killer: fragile payment controls? I’ve seen multi-million dollar institutions blindsided because they missed a critical step. Don’t be next.
Here are 10 battlefield-tested strategies to fortify your payment defenses – the same ones I use with leading banks and fintech. This isn’t just theory; it’s about protecting your bottom line and reputation.
1. The Two-Person Rule: Strong Authorization & Segregation (Maker and Checker)
– Never one pair of hands: Enforce Maker–Checker / 4-eyes principle.
– Clear lanes: Separate roles for initiation, approval, & release.
– No ghost IDs: Avoid shared or generic user IDs.
2. Precision Access (ACL): Role-Based & Identity Controls
– Need-to-know access: Apply least-privilege.
– Your digital fortress: MFA for ALL payment actions.
– Regular check-ups: Periodic access reviews & certifications.
3. Guardrails for Cash: Limits & Threshold Controls
— Cap your exposure: Define transaction, daily, & monthly limits.
– Stop the deluge: Set velocity limits (payments per time window).
– Smart caps: Dynamic limits based on risk level.
4. The Early Warning System: Real-Time Monitoring & Fraud Detection
– Catch it live: Monitor payments in real time, not after the fact.
– Brains & Brawn: Use rules + behavioral analytics.
– Red flags: Trigger alerts for anomalies (new beneficiary, unusual amount, geo changes).
5. The Approval Gauntlet: Workflow Controls
– Risk-calibrated: Higher amount = more approvals.
– Mandatory unlocks for:
– New beneficiaries
– Limit changes
– Urgent or off-cycle payments
6. The Indelible Record: Auditability & Traceability
– Every move logged: Maintain end-to-end audit trails.
– The 5 W’s:Log who, what, when, where, and why.
– Tamper-proof:** Ensure logs are immutable and secure.
7. Digital Fort Knox: Data Protection & Security
– Scramble it all: Encrypt payment data in transit and at rest.
– Mask the sensitive: Use tokenization for identifiers.
– Behind the curtain: Mask data in logs and non-production.
8. The Stress Test: Control Testing & Assurance
– Always checking: Perform regular control testing.
– Break it to fix it: Simulate fraud and failure scenarios.
– Prioritize: Track control defects as high-priority risks.
9. Smart Automation, Safer Automation: Automation with Guardrails
– Streamline low-risk: Automate common payments.
– Human in Loop: Keep human approval for high-risk events.
– AI accountability: Monitor AI/automation decisions with explainability.
10. Who Owns What? Governance & Ownership
– No grey areas: Clearly define control owners.
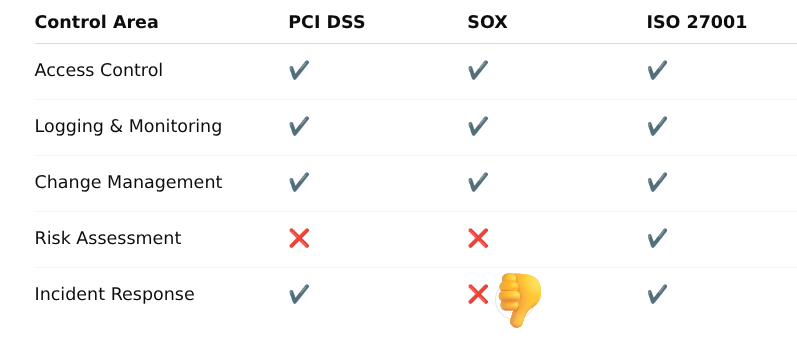
— Stay compliant: Align with PCI DSS, SOX, ISO 27001, RBI/FFIEC.
– Adapt or die: Review controls when products, channels, or regulations change.
The Unbreakable Rule:
Payment controls should be preventive first, detective second, and corrective last. Your goal is to stop the problem before it starts.
Which of these controls keeps you up at night the most, and why are you finding it a challenge?
Which of these controls keeps you up at night the most, and why are you finding it a challenge?
| Control Area | Why It Matters in Payments |
| —————————————- | —————————————— |
| Access Control | Prevent fraud & unauthorized fund movement |
| Logging & Monitoring | Trace disputes, fraud, and SLA breaches |
| Change Management | Avoid silent production defects |
| Risk Assessment | Prioritize high-value payment rails |
| Incident Response | Reduce blast radius of payment outages |